
Executive Summary
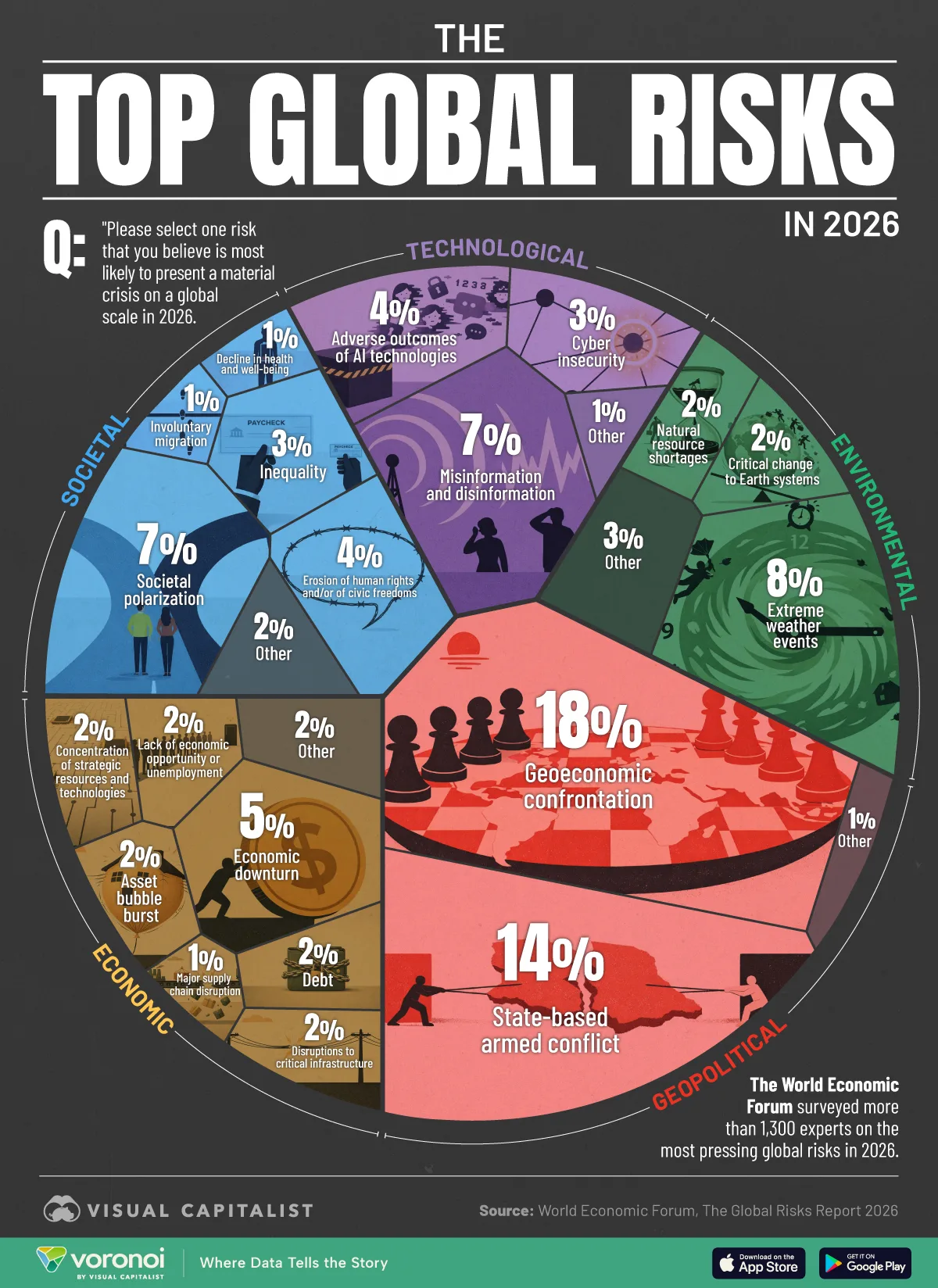
In 2026, misinformation and disinformation have moved from being a “communications issue” to a core enterprise risk. The World Economic Forum (WEF) describes today’s environment as an “age of competition,” where fragmentation, confrontation, and distrust amplify risk across geopolitics, economics, and society. In the WEF Global Risks Perception Survey, more than 1,300 experts identified the risks most likely to trigger a material global crisis in 2026, with geoeconomic confrontation at the top—and mis/disinformation and societal polarization featuring prominently among near-term risks.
For organisations, the threat is not limited to fake news. It includes deepfakes targeting executives, manipulated documents, coordinated smear campaigns, counterfeit websites, “fraud by persuasion,” and the rapid spread of misleading narratives during real operational incidents (e.g., outages, recalls, weather disruptions, cyber events). The business consequences are measurable: customer churn, investor confidence shocks, regulatory exposure, supply chain disruption, fraud losses, and higher insurance and financing friction.
This article provides a practical, board-ready framework to manage mis/disinformation risk in 2026:
-
define the threat surface, 2) map the business impact pathways, 3) implement governance and controls across people/process/technology, 4) build a rapid response playbook, and 5) stress-test your organisation’s “trust resilience” using scenarios. Composite (anonymised) case studies illustrate how mid-market organisations can reduce losses and recover faster—without over-engineering.
1) Why Misinformation Is a Material Business Risk in 2026
The speed, scale, and plausibility of false narratives have changed. In practical terms:
-
Speed: Social platforms, messaging apps, and AI-generated content can move faster than corporate approval chains.
-
Scale: One false claim can be replicated thousands of times across channels, sometimes by automated networks.
-
Plausibility: Voice clones, synthetic video, and convincing “document forgeries” reduce the natural skepticism people once had.
The WEF’s framing matters for boards: the world is operating in an environment where competitive pressure and distrust are intensifying. In such conditions, “truth” becomes contested and operational decisions become harder—especially during crises.
What mis/disinformation looks like in business reality
Mis/disinformation is not only about politics. Common corporate manifestations include:
-
Executive impersonation (voice notes, video calls) instructing urgent payments or sensitive disclosures
-
Counterfeit brand assets (fake websites, fake social pages, fake customer support numbers)
-
Manipulated “leaks” (edited emails, partial screenshots, fabricated internal memos)
-
False safety or quality claims about products
-
Supply chain rumors (“port shutdown,” “supplier bankrupt,” “contamination”)
-
Crisis distortion during real incidents (cyber breach, outage, weather disruption)
-
Coordinated review attacks and reputational sabotage
-
Internal misinformation (staff rumors that damage morale, cause attrition, or trigger operational errors)
2) The Business Impact Pathways: How Misinformation Becomes a Loss Event
Boards often struggle to prioritise mis/disinformation because it feels intangible. The key is to translate it into loss pathways. There are five dominant ones:
A) Revenue and customer trust loss
-
Drop in conversions, cancellations, reduced repeat purchases
-
Customer service overload and SLA breaches
-
Channel partners pausing orders “until clarity”
Red flag: a customer-facing incident becomes “two incidents”—the operational event and the narrative event.
B) Financial fraud and payment diversion
Disinformation is increasingly used to create urgency and bypass controls (“CEO needs this today,” “supplier banking changed,” “confidential acquisition”).
Red flag: urgent payment requests with “do not call” instructions.
C) Regulatory and legal exposure
-
Consumer protection issues (false claims and misinformation about product safety)
-
Market disclosure risk (rumors affecting investor behavior)
-
Data protection risk if fake portals harvest customer credentials
Red flag: misinformation triggers reactive statements that later become inconsistent with facts.
D) Operational disruption
-
Staff confusion, inconsistent execution of procedures
-
Supplier panic, hoarding, delayed shipments
-
Security incidents triggered by phishing/impersonation
Red flag: internal channels become noisy, with conflicting instructions and “forwarded facts.”
E) Strategic and reputational damage
-
Loss of confidence from lenders, insurers, and institutional partners
-
Negative media cycles that outlast the original issue
Red flag: reputational impacts worsen after the organisation “fixes the technical problem.”
3) The Risk Surface: Where Your Organisation Is Exposed
A practical exposure map typically includes:
1) External narrative channels
-
Social platforms and public web
-
Messaging apps where false claims spread quickly
-
Media reporting and commentary ecosystems
2) Digital identity and brand assets
-
Domain names, subdomains, social handles
-
“Lookalike” domains and fake landing pages
-
Customer support numbers and WhatsApp impersonation
3) Key individuals
-
CEO/CFO and finance approvers
-
Sales leaders and relationship managers
-
Legal/compliance and HR decision-makers
4) Third parties and supply chain
-
Vendors with access to invoices, payment details, customer data
-
Logistics providers whose status updates shape customer expectations
5) Internal communication environment
-
Staff chat groups, email chains, informal “knowledge networks”
-
Weak change control for operational instructions
4) Governance: Assign Ownership Before the Incident Happens
Mis/disinformation risk collapses when everyone assumes someone else owns it.
A workable governance model
-
Board / Risk Committee: sets risk appetite for “trust events” (acceptable downtime, acceptable reputational exposure, crisis disclosure posture)
-
Executive sponsor: often COO, CRO, or a combined Risk/Compliance leader
-
Operational owner: Communications + Security + Legal + Customer Ops (a standing “Trust Response Cell”)
-
Incident commander: named role with authority during a trust event (not necessarily the CEO)
-
RACI clarity: who approves statements, who validates facts, who engages regulators, who handles customer comms
This is the same maturity leap organisations made with cyber risk: stop treating it as “IT’s problem” and treat it as a business continuity issue.
5) Controls That Actually Work: People, Process, Technology
The best approach is layered: you cannot “tool” your way out of a human trust problem.
People controls
-
Executive impersonation training for finance, HR, and assistants
-
Two-channel verification discipline: “If it arrives in email, verify via phone; if it arrives via phone, verify via another channel.”
-
Crisis communication drills so leaders don’t freeze or improvise contradictory statements
-
Internal rumor management: managers trained to address uncertainty quickly with known facts
Process controls
-
Payment controls hardened for persuasion attacks
-
verified bank change process (with call-back to known numbers)
-
dual approvals for exceptions
-
“no exceptions” rule during high-risk periods (e.g., after a public rumor spikes)
-
-
Content and statement approval workflow
-
pre-approved holding statements
-
fact validation checklist
-
legal review triggers
-
-
Supplier and partner protocols
-
standard “truth channel” for updates
-
contract clauses on incident notification and public statements
-
-
Domain and brand hygiene
-
secure key domains
-
monitor lookalike domains
-
verify official handles and pages
-
Technology controls (targeted, not vanity)
-
Brand monitoring for sudden spikes in mentions and sentiment shifts
-
Domain monitoring for lookalikes and phishing portals
-
Email security and DMARC/DKIM/SPF to reduce spoofing
-
Deepfake and voice-clone risk handling (policy + verification, not only detection)
-
Incident collaboration tooling to keep internal truth consistent (single source of truth)
Important: detection helps—but response discipline is what prevents financial and reputational compounding.
6) Crisis Response: A “Trust Incident” Playbook
A mis/disinformation incident should trigger an operational playbook like any other crisis.
Phase 1: Triage (first 30–60 minutes)
-
Confirm: Is this misinformation, disinformation, impersonation, or a real incident being distorted?
-
Lock down: freeze sensitive actions (payments, public statements) until verification
-
Activate: Trust Response Cell + incident commander
Phase 2: Validate facts (same-day)
-
Establish a single source of truth internally
-
Collect evidence (screenshots, URLs, timestamps)
-
Engage platform takedown where applicable
-
Identify affected stakeholders (customers, staff, regulators, partners)
Phase 3: Communicate (fast, consistent, measured)
-
Issue a short holding statement if needed: “We are aware… investigating… here is the official channel…”
-
Keep internal staff aligned: “what we know / what we don’t / what to do”
-
Provide customer service scripts to prevent contradictory messaging
Phase 4: Recover and learn
-
Post-incident review with metrics: time to containment, financial loss avoided, customer churn, sentiment recovery time
-
Improve controls, training, monitoring thresholds
7) Composite Case Study 1: Invoice Diversion via Executive Impersonation
Profile: Caribbean-based importer/distributor, high transaction volume, multiple suppliers.
Incident: Finance receives an urgent voice note “from the CEO” requesting an immediate transfer to “secure inventory.” The voice is convincing, language matches the CEO, and the message pressures secrecy.
What happened:
-
The team initiated payment steps, but a junior analyst noticed the request bypassed the normal procurement workflow.
-
A secondary verification call to the CEO’s known number exposed it as a fraud attempt.
Root cause findings:
-
No formal “voice instruction verification” rule
-
No training that voice cloning is now a credible threat
-
Payment exceptions process was too informal
Controls implemented:
-
Two-channel verification required for any “urgent executive” request
-
“No secrecy” rule—if secrecy is demanded, it triggers escalation
-
Pre-approved crisis/fraud escalation tree for finance
Result:
-
Fraud avoided; subsequent phishing attempts reduced in success due to hardened behaviors.
Lesson: In 2026, trust is a control environment. If the control is weak, the attacker doesn’t need malware—only persuasion.
8) Composite Case Study 2: False Product Safety Claim Triggering Customer Panic
Profile: Consumer-facing company with strong brand visibility.
Incident: A viral post claims the company’s product caused harm and alleges a cover-up. The claim spreads rapidly with edited images and fabricated “reports.”
Impact:
-
Customer service volumes triple within hours
-
Retailers request clarification and temporarily pause reorders
-
Staff begin sharing “inside info” speculations on private groups
Response gaps discovered:
-
No pre-written holding statement
-
No “truth hub” page to anchor official updates
-
Slow legal review created a silence vacuum
Controls implemented:
-
Crisis comms playbook with pre-approved templates
-
Dedicated “official updates” page linked in all responses
-
Retailer communications protocol (single contact, daily update schedule)
-
Internal staff briefing script: what to say, what not to say, where to direct inquiries
Result:
-
Narrative stabilized faster; retail disruption shortened; internal confusion reduced.
Lesson: When you don’t fill the information space quickly, someone else will.
9) Metrics That Boards Actually Care About
To govern this risk, avoid vanity metrics (“mentions,” “likes”). Use resilience metrics:
-
Time-to-detect (minutes/hours from spike to escalation)
-
Time-to-validate facts (how quickly truth is established internally)
-
Time-to-first statement (when appropriate)
-
Customer contact deflection rate (how many inquiries are resolved via official channels)
-
Fraud loss avoided / reduced through verification controls
-
Sentiment recovery time
-
Churn impact after the incident
-
Supplier/partner confidence (measured by reorder normalization)
10) A 30–60–90 Day Roadmap for Mis/Disinformation Resilience
First 30 days: Baseline and quick wins
-
Map brand and executive impersonation exposure
-
Harden payment verification processes
-
Secure domains and verify official social handles
-
Define the Trust Response Cell and escalation process
Days 31–60: Build the playbooks
-
Create the trust incident playbook (triage, validation, comms, takedown)
-
Pre-approve statement templates + customer scripts
-
Implement monitoring thresholds and evidence capture procedures
Days 61–90: Test and integrate
-
Run tabletop exercises (fraud impersonation + viral rumor + crisis distortion)
-
Align with cyber incident response and business continuity planning
-
Formalize third-party expectations (suppliers, PR, legal, insurers)
How Dawgen Global Risk Advisory Services Can Help
Dawgen Global helps organisations convert abstract “trust threats” into measurable, manageable operational risk. Our support typically includes:
-
Mis/Disinformation Risk Diagnostic (exposure mapping + control review)
-
Executive impersonation and payment diversion control hardening
-
Trust Incident Response Playbooks (comms + security + legal alignment)
-
Scenario stress testing (reputation + cashflow + continuity)
-
Tabletop exercises and crisis simulations
-
Monitoring and governance design for board-level oversight
Next Step!
In 2026, mis/disinformation is not a side risk—it is a multiplier that can turn routine incidents into brand and cashflow crises. If your organisation has not tested its trust response under pressure, you are relying on hope and improvisation.
Let’s build your misinformation resilience program—practical, tested, and aligned to business continuity.
🔗 Contact us: https://www.dawgen.global/contact-us/
📧 [email protected]
📞 USA: 855-354-2447
💬 WhatsApp Global: +1 555 795 9071
About Dawgen Global
“Embrace BIG FIRM capabilities without the big firm price at Dawgen Global, your committed partner in carving a pathway to continual progress in the vibrant Caribbean region. Our integrated, multidisciplinary approach is finely tuned to address the unique intricacies and lucrative prospects that the region has to offer. Offering a rich array of services, including audit, accounting, tax, IT, HR, risk management, and more, we facilitate smarter and more effective decisions that set the stage for unprecedented triumphs. Let’s collaborate and craft a future where every decision is a steppingstone to greater success. Reach out to explore a partnership that promises not just growth but a future beaming with opportunities and achievements.







Join hands with Dawgen Global. Together, let’s venture into a future brimming with opportunities and achievements

