Borderless Assurance: Internal Audit That Moves at the Speed of Risk
Powered by Dawgen Global’s IAVANTAGE™ Framework
Executive Summary
-
Caribbean organisations are increasingly “networked businesses”—built on vendors, outsourcers, cloud providers, fintech partners, logistics providers, payroll processors, and consultants. When these relationships fail, the business fails. That makes third-party risk a board-level risk, not a procurement issue.
-
Many organisations still manage third-party risk with fragmented practices: procurement checks, contract clauses, occasional vendor meetings, and compliance questionnaires. These are necessary—but rarely sufficient to produce assurance.
-
Internal Audit can close the gap by providing independent, audit-grade assurance over the third-party lifecycle: onboarding, due diligence, contracting, access governance, performance monitoring, incident response, and exit/offboarding.
-
The “Borderless Assurance” approach is especially relevant here: third-party ecosystems are cross-border by nature, and assurance must scale across multiple entities and jurisdictions.
-
Dawgen Global’s IAVANTAGE™ Framework structures third-party assurance around value outcomes (protective, operational, strategic, stakeholder) and delivers it through repeatable modules and a digital, borderless model (co-sourced, outsourced, or hybrid).
1) Why third-party risk has become a Caribbean board priority
In many Caribbean organisations, “the business” now includes:
-
payroll and HR platforms
-
outsourced IT and managed security services
-
cloud hosting and SaaS systems
-
card processors and fintech integrations
-
logistics providers and distributors
-
customer support BPOs
-
consultants and contractors with sensitive access
-
critical suppliers with single-source concentration
This is not merely outsourcing. It is the operating model.
That creates a simple risk truth:
Your risk posture is only as strong as your weakest third party.
When third parties fail, the consequences are rarely isolated:
-
data breaches and privacy violations
-
business interruption
-
regulatory exposure
-
fraud and financial loss
-
reputational damage
-
contractual disputes and unexpected costs
-
operational bottlenecks and customer attrition
In a region where multi-entity groups operate across islands, third-party dependencies can become systemic. One vendor can impact multiple entities at once.
2) Third-party risk is often mismanaged because it’s treated as “procurement work”
Many organisations manage third-party risk primarily through procurement:
-
vendor selection
-
contracting
-
price negotiation
-
basic compliance checks
-
periodic performance meetings
Procurement is essential. But procurement governance is not assurance.
Boards need answers to questions procurement alone cannot confidently answer:
-
Does this third party actually meet our security and resilience requirements?
-
Are controls operating effectively or just documented?
-
Can the vendor recover quickly after a disruption?
-
Do they have sub-contractors (fourth parties) that create hidden risk?
-
Is our access governance preventing vendors from becoming attack vectors?
-
If a breach happens, can we respond quickly and credibly?
-
Are we monitoring ongoing risk—or only assessing at onboarding?
That is the space where Internal Audit adds unique value.
3) The “third-party lifecycle” approach: audit what matters, when it matters
Internal Audit should not treat third-party risk as a single annual audit. The better approach is lifecycle-based assurance.
Stage 1 — Planning and classification (before selection)
Key question: Do we know which vendors are truly critical?
Audit focus:
-
vendor criticality classification (financial, operational, regulatory, cyber)
-
concentration risk and single points of failure
-
minimum standards by tier (critical/high/medium/low)
-
governance and accountability (who owns each relationship)
Stage 2 — Due diligence (before contracting)
Key question: Are we selecting vendors with evidence—not assumptions?
Audit focus:
-
due diligence completeness and validation
-
financial stability checks
-
cyber and privacy posture (for data/IT vendors)
-
resilience capability (BCP/DR evidence)
-
regulatory considerations
-
fourth-party awareness (sub-contractors)
Stage 3 — Contracting (risk embedded in legal terms)
Key question: Does the contract protect us when things go wrong?
Audit focus:
-
security requirements and breach notification clauses
-
audit rights and access to assurance reports
-
SLAs aligned to business needs
-
right to terminate and exit support
-
data ownership and retention
-
subcontracting restrictions and approvals
-
penalties and remedies for non-performance
Stage 4 — Access governance and onboarding controls
Key question: Do vendors have only the access they need—no more, no longer?
Audit focus:
-
least privilege access
-
time-bound and monitored vendor access
-
privileged access controls
-
segregation of duties implications
-
onboarding and offboarding discipline
-
access logs reviewed and evidenced
Stage 5 — Ongoing monitoring (where most programs fail)
Key question: Are we monitoring risk continuously—or only when something goes wrong?
Audit focus:
-
SLA monitoring and reporting discipline
-
incident reporting and escalation
-
periodic assurance reports (SOC, ISO, internal testing)
-
performance trend analysis
-
issue management and remediation follow-up
-
contract compliance checks
Stage 6 — Incident response and breach readiness
Key question: If the vendor fails or is breached, are we ready?
Audit focus:
-
joint incident response playbooks
-
contact lists and escalation paths
-
breach notification timeliness
-
forensic cooperation requirements
-
communications and regulator reporting plans
-
tabletop exercises / simulations
Stage 7 — Exit/offboarding (often ignored until crisis)
Key question: Can we exit without disruption or data loss?
Audit focus:
-
exit plans
-
data return and deletion evidence
-
transition support obligations
-
knowledge transfer
-
continuity arrangements and fallback options
This lifecycle framework turns third-party risk from “a checklist” into an assurance program.
4) The Caribbean risk hotspots internal audit should prioritise
Based on recurring regional realities, Internal Audit should focus on these third-party risk hotspots first:
-
Outsourced IT / managed service providers (security, access, resilience)
-
Cloud and SaaS providers (configurations, data protection, recovery)
-
Payment processors / fintech partnerships (fraud, compliance, uptime)
-
Payroll and HR processors (data privacy, integrity, access)
-
Critical suppliers with single-source dependence (continuity risk)
-
BPO / customer service vendors (data access, quality, compliance)
-
Consultants and contractors with privileged access (access governance)
5) How IAVANTAGE™ makes third-party assurance a value engine (not just risk reporting)
Third-party assurance is not about writing “vendor findings.” It is about protecting value creation.
IAVANTAGE™ helps Internal Audit translate vendor risk into enterprise value outcomes:
Protective Value: prevent loss events
-
reduce likelihood of breach incidents via improved access governance
-
reduce fraud exposure via stronger vendor controls
-
reduce regulatory penalties via compliance-aligned contracting and monitoring
Operational Value: improve continuity and performance
-
fewer outages and faster recovery
-
better vendor performance management
-
reduced rework from failed service delivery
-
improved procurement efficiency through tiered standards
Strategic Value: enable growth and transformation safely
-
assurance over digital transformations powered by vendors
-
faster onboarding of partners with repeatable assurance modules
-
reduced risk in cross-border expansions and integrations
Stakeholder Value: credibility with regulators and customers
-
demonstrable governance
-
evidence-based assurance over critical vendors
-
improved trust outcomes after incidents
This is where Boards start to see IA not as “police” but as a protector of execution and trust.
6) The Dawgen “Borderless Assurance” model for third-party risk
Third-party risk is inherently cross-border, which makes it ideal for a borderless delivery model.
6.1 Repeatable assurance modules (“vendor assurance packs”)
Dawgen can deploy standard modules such as:
-
vendor governance and tiering review
-
cyber access governance review
-
SLA and performance monitoring review
-
contract risk clause review (with legal alignment where applicable)
-
resilience and DR evidence validation
-
incident response readiness review
-
offboarding and exit readiness review
These modules create consistency across entities, while allowing local tailoring.
6.2 Digital layer: evidence discipline at speed
Borderless delivery relies on:
-
secure client portal for evidence collection
-
standardised workpapers and templates
-
version control and audit trail
-
analytics where relevant (e.g., SLA trends, incident patterns)
-
dashboards for audit committee reporting
6.3 Flexible delivery options
-
Co-sourced: Dawgen provides specialist capacity + modules while your IA retains leadership
-
Outsourced: Dawgen runs third-party risk assurance under a governed charter
-
Hybrid: In-house team covers core audits; Dawgen handles high-risk vendor assurance and cyber-linked third-party audits
7) What “good” third-party assurance testing looks like (practical audit tests)
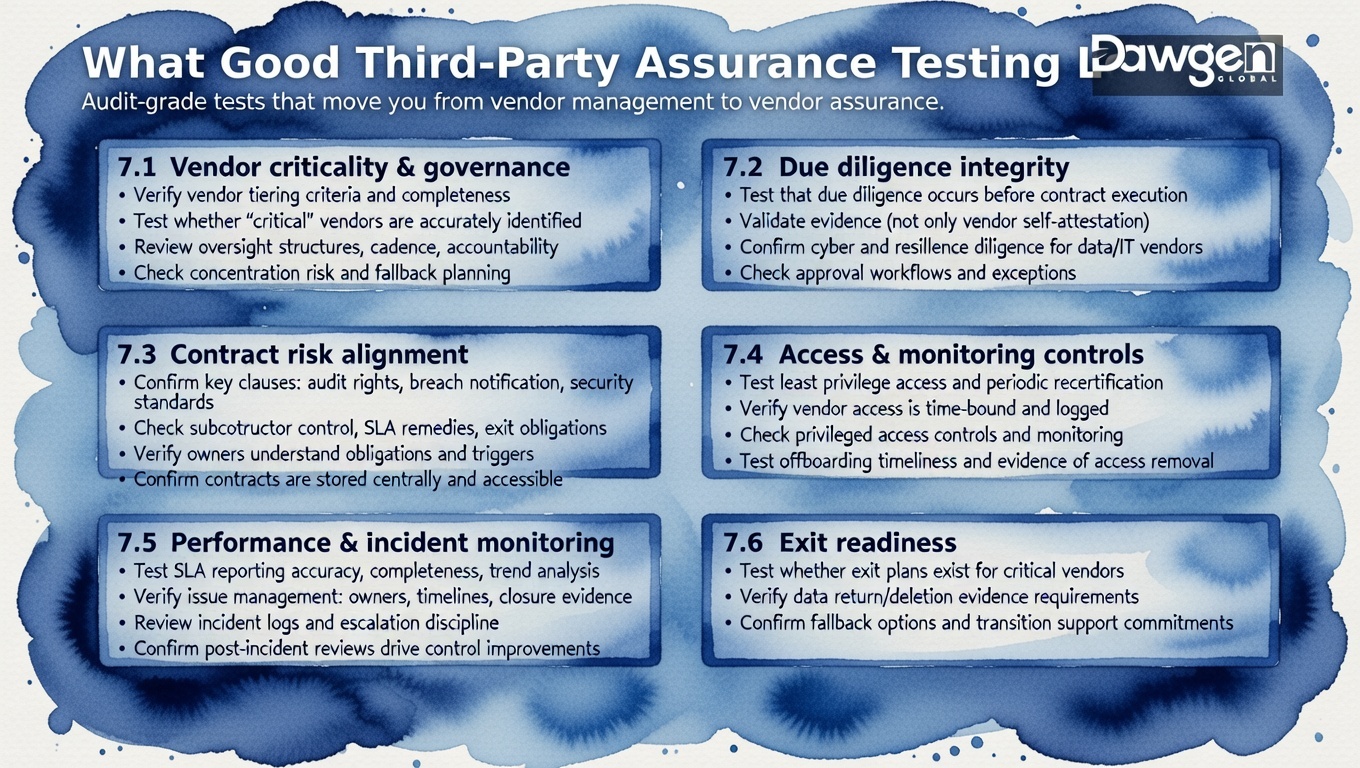
Below are audit-grade tests that create confidence:
7.1 Vendor criticality and governance
-
verify vendor tiering criteria and completeness
-
test whether “critical” vendors are accurately identified
-
review oversight structures, reporting cadence, and accountability
-
check concentration risk and fallback planning
7.2 Due diligence integrity
-
test that due diligence is performed before contract execution
-
validate evidence (not only vendor self-attestation)
-
confirm cyber and resilience due diligence for data/IT vendors
-
check approval workflows and exceptions
7.3 Contract risk alignment
-
test presence and enforceability of key clauses: audit rights, breach notification, security standards, subcontractor control, SLA remedies, exit obligations
-
verify contract owners understand obligations and triggers
-
confirm contracts are stored centrally and accessible
7.4 Access and monitoring controls
-
test least privilege access and recertification for vendor accounts
-
verify vendor access is time-bound and logged
-
check privileged access controls and monitoring
-
test offboarding timeliness and evidence of access removal
7.5 Performance and incident monitoring
-
test SLA reporting: accuracy, completeness, trend analysis
-
verify issue management: owners, timelines, closure evidence
-
review incident logs and escalation discipline
-
confirm post-incident reviews lead to control improvements
7.6 Exit readiness
-
test whether exit plans exist for critical vendors
-
verify data return/deletion evidence requirements
-
confirm fallback options and transition support commitments
These tests move organisations from “vendor management” to “vendor assurance.”
8) Composite Caribbean case vignettes
Case A — The vendor access exposure
A multi-entity group relied on an MSP. Vendor admin access was broad and long-lived.
Audit assurance results:
-
privileged access not time-bound
-
access recertification incomplete
-
monitoring weak
Outcome:
-
reduced breach exposure, improved governance, board confidence increased.
Case B — SLA reporting without real assurance
A customer-facing service had monthly SLA reports, but outages persisted.
Audit assurance results:
-
SLA reports didn’t measure what mattered (impact, root cause)
-
no penalties enforced
-
no trend-based corrective action
Outcome:
-
improved SLA design, strengthened accountability, measurable uptime improvements.
Case C — Exit crisis
A vendor relationship deteriorated, but the organisation had no exit plan.
Audit assurance results:
-
no documented exit plan
-
data deletion requirements unclear
-
transition support not contractually secured
Outcome:
-
exit readiness developed; future vendor contracts strengthened.
9) Reporting third-party assurance to the board: a clearer dashboard
Boards need a single view of vendor risk that is:
-
prioritised
-
evidence-based
-
actionable
A Board-ready third-party dashboard should include:
-
list of critical vendors and tiering
-
assurance status (assured / partially assured / not assured)
-
key risk themes (cyber access, resilience, compliance, performance)
-
incidents and near misses
-
remediation commitments (vendor + internal owner)
-
trend indicators (improving / stable / deteriorating)
-
exit readiness status for critical vendors
10) Audit committee toolkit: 10 questions that reveal hidden vendor risk
-
Which vendors are truly critical—and do we agree on the list?
-
Which critical vendors have current assurance, not just questionnaires?
-
Who owns each relationship—and how do they report performance?
-
Do we have audit rights and timely breach notification clauses?
-
Who has vendor privileged access—and how is it monitored?
-
Are we monitoring SLA trends or only receiving monthly reports?
-
Are subcontractors (fourth parties) disclosed and governed?
-
When did we last test vendor recovery and resilience evidence?
-
Do we have an exit plan for each critical vendor?
-
If a breach happens tomorrow, do we have a joint response playbook?
If these questions cannot be answered confidently, the vendor risk program is likely too thin.
11) A 90-day third-party assurance plan (fast and measurable)
Weeks 1–2: Establish the “critical vendor map”
-
confirm vendor inventory and criticality tiering
-
identify top 10 critical vendors by risk impact
-
define assurance scope and standards by tier
-
confirm board expectations and reporting format
Weeks 3–8: Execute 2–3 high-impact vendor assurance modules
-
vendor access governance (IAM/PAM focus for vendors)
-
resilience and recovery evidence validation
-
contract clause and audit rights review
-
SLA and issue management review
Weeks 9–12: Implement monitoring and board dashboard
-
implement vendor assurance dashboard
-
create remediation follow-up cadence
-
embed exit readiness requirements for critical vendors
-
define ongoing assurance rhythm (quarterly, semi-annual)
By day 90, Boards should see: better visibility, clearer accountability, fewer surprises.
Third-party risk is now a core risk domain—and Internal Audit is the assurance engine
Third-party ecosystems are not peripheral. They are fundamental to how Caribbean organisations operate and grow.
That is why third-party risk is business risk—and why Internal Audit must provide independent assurance that third-party controls, governance, and resilience are real, evidenced, and improving.
This is precisely what Borderless Assurance enables: scalable, repeatable third-party assurance across the Caribbean—powered by IAVANTAGE™ and delivered digitally without requiring permanent overhead.
Next Step!
If you want board-ready assurance over your critical vendors and outsourcing ecosystem, start with a Dawgen Third-Party Assurance Diagnostic, aligned to IAVANTAGE™:
-
vendor criticality mapping and assurance gaps
-
top 10 vendor risk review
-
2–3 high-impact assurance modules (access, resilience, contracting, monitoring)
-
board dashboard and remediation cadence
-
option to deploy a borderless audit pod (co-sourced / outsourced / hybrid)
🔗 Contact form: https://www.dawgen.global/contact-us/
📧 Email: [email protected]
📞 Caribbean: 876-9293670 | 876-9293870
📞 💬 WhatsApp Global: +1 555 795 9071
“Embrace BIG FIRM capabilities without the big firm price at Dawgen Global, your committed partner in carving a pathway to continual progress in the vibrant Caribbean region. Our integrated, multidisciplinary approach is finely tuned to address the unique intricacies and lucrative prospects that the region has to offer. Offering a rich array of services, including audit, accounting, tax, IT, HR, risk management, and more, we facilitate smarter and more effective decisions that set the stage for unprecedented triumphs. Let’s collaborate and craft a future where every decision is a steppingstone to greater success. Reach out to explore a partnership that promises not just growth but a future beaming with opportunities and achievements.







Join hands with Dawgen Global. Together, let’s venture into a future brimming with opportunities and achievements

